
A beforehand undetected piece of malware discovered on virtually 30,000 Macs worldwide is producing intrigue in safety circles, that are nonetheless making an attempt to know exactly what it does and what objective its self-destruct functionality serves.
As soon as an hour, contaminated Macs verify a management server to see if there are any new instructions the malware ought to run or binaries to execute. To this point, nonetheless, researchers have but to look at supply of any payload on any of the contaminated 30,000 machines, leaving the malware’s final purpose unknown. The dearth of a remaining payload means that the malware might spring into motion as soon as an unknown situation is met.
Additionally curious, the malware comes with a mechanism to fully take away itself, a functionality that’s usually reserved for high-stealth operations. To this point, although, there are not any indicators the self-destruct function has been used, elevating the query why the mechanism exists.
Moreover these questions, the malware is notable for a model that runs natively on the M1 chip that Apple launched in November, making it solely the second identified piece of macOS malware to take action. The malicious binary is extra mysterious nonetheless, as a result of it makes use of the macOS Installer JavaScript API to execute instructions. That makes it onerous to research set up package deal contents or the way in which that package deal makes use of the JavaScript instructions.
The malware has been present in 153 nations with detections concentrated within the US, UK, Canada, France, and Germany. Its use of Amazon Net Companies and the Akamai content material supply community ensures the command infrastructure works reliably and likewise makes blocking the servers more durable. Researchers from Purple Canary, the safety agency that found the malware, are calling the malware Silver Sparrow.
Fairly severe menace
“Although we haven’t noticed Silver Sparrow delivering extra malicious payloads but, its forward-looking M1 chip compatibility, international attain, comparatively excessive an infection fee, and operational maturity counsel Silver Sparrow is a fairly severe menace, uniquely positioned to ship a doubtlessly impactful payload at a second’s discover,” Purple Canary researchers wrote in a blog post printed on Friday. “Given these causes for concern, within the spirit of transparency, we wished to share the whole lot we all know with the broader infosec trade sooner relatively than later.”
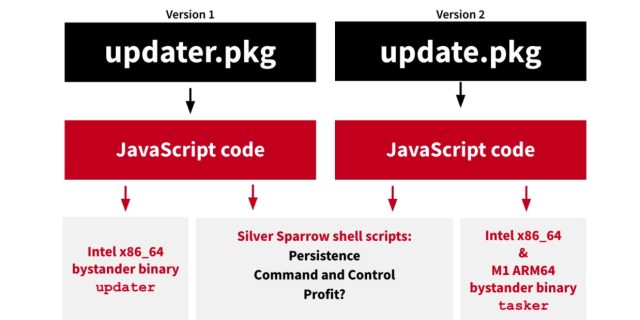
Silver Sparrow is available in two variations—one with a binary in mach-object format compiled for Intel x86_64 processors and the opposite Mach-O binary for the M1. The picture under presents a high-level overview of the 2 variations:
Purple Canary
To this point, researchers haven’t seen both binary do a lot of something, prompting the researchers to seek advice from them as “bystander binaries.” Curiously, when executed, the x86_64 binary shows the phrases “Whats up World!” whereas the M1 binary reads “You probably did it!” The researchers suspect the information are placeholders to present the installer one thing to distribute content material outdoors the JavaScript execution. Apple has revoked the developer certificates for each bystander binary information.
Silver Sparrow is just the second piece of malware to comprise code that runs natively on Apple’s new M1 chip. An adware pattern reported earlier this week was the primary. Native M1 code runs with better velocity and reliability on the brand new platform than x86_64 code does as a result of the previous doesn’t must be translated earlier than being executed. Many builders of reliable macOS apps nonetheless haven’t accomplished the method of recompiling their code for the M1. Silver Sparrow’s M1 model suggests its builders are forward of the curve.
As soon as put in, Silver Sparrow searches for the URL the installer package deal was downloaded from, most probably so the malware operators will know which distribution channels are most profitable. In that regard, Silver Sparrow resembles beforehand seen macOS adware. It stays unclear exactly how or the place the malware is being distributed or the way it will get put in. The URL verify, although, means that malicious search outcomes could also be a minimum of one distribution channel, by which case, the installers would possible pose as reliable apps.
Among the many most spectacular issues about Silver Sparrow is the variety of Macs it has contaminated. Purple Canary researchers labored with their counterparts at Malwarebytes, with the latter group discovering Silver Sparrow put in on 29,139 macOS endpoints as of Wednesday. That’s a big achievement.
“To me, essentially the most notable [thing] is that it was discovered on virtually 30K macOS endpoints… and these are solely endpoints the MalwareBytes can see, so the quantity is probably going means larger,” Patrick Wardle, a macOS safety professional, wrote in an Web message. “That’s fairly widespread… and but once more reveals the macOS malware is changing into ever extra pervasive and commonplace, regardless of Apple’s finest efforts.”
For many who need to verify if their Mac has been contaminated, Purple Canary supplies indicators of compromise on the finish of its report.

